Question: The GSM authentication protocol is illustrated below. Is the mobile authenticated? Is the base station authenticated? Justify your answers. A fake base station attack relies
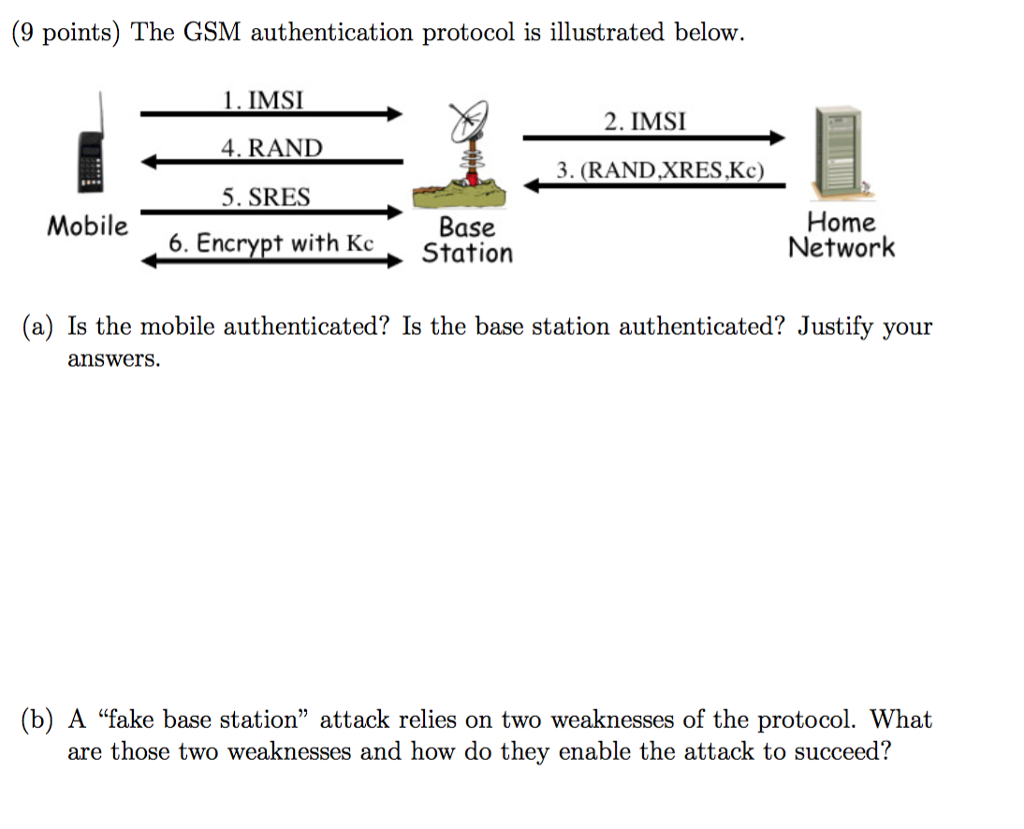
The GSM authentication protocol is illustrated below. Is the mobile authenticated? Is the base station authenticated? Justify your answers. A "fake base station" attack relies on two weaknesses of the protocol. What are those two weaknesses and how do they enable the attack to succeed
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


