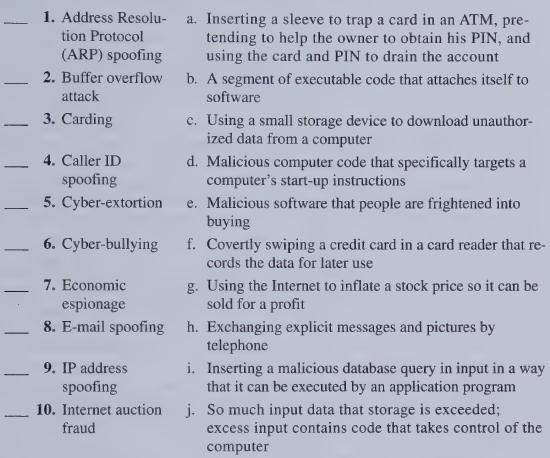
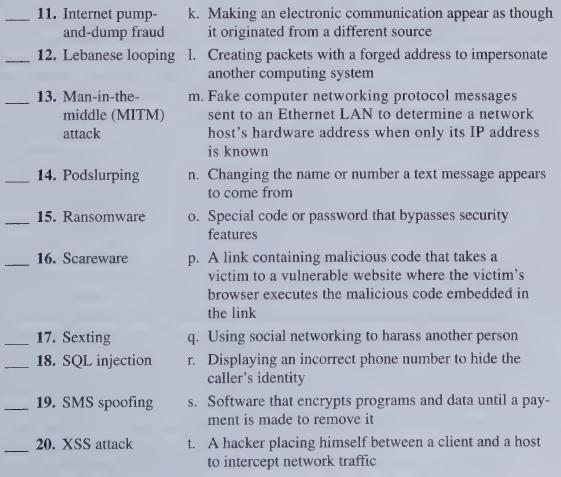
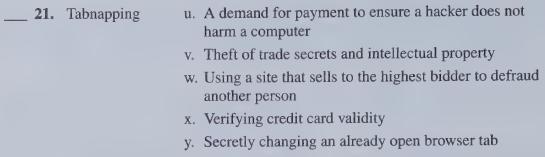
Computer Fraud and Abuse Techniques. Match the computer fraud and abuse technique in the left column with
Question:
Computer Fraud and Abuse Techniques.
Match the computer fraud and abuse technique in the left column with the scenario in the right column. Terms on the left may be used once, more than once, or not at all.
Transcribed Image Text:
- - - - 1. Address Resolu- tion Protocol (ARP) spoofing 2. Buffer overflow attack 3. Carding 4. Caller ID spoofing 5. Cyber-extortion 6. Cyber-bullying 7. Economic espionage 8. E-mail spoofing 9. IP address spoofing 10. Internet auction fraud a. Inserting a sleeve to trap a card in an ATM, pre- tending to help the owner to obtain his PIN, and using the card and PIN to drain the account b. A segment of executable code that attaches itself to software c. Using a small storage device to download unauthor- ized data from a computer d. Malicious computer code that specifically targets a computer's start-up instructions e. Malicious software that people are frightened into buying f. Covertly swiping a credit card in a card reader that re- cords the data for later use g. Using the Internet to inflate a stock price so it can be sold for a profit h. Exchanging explicit messages and pictures by telephone i. Inserting a malicious database query in input in a way that it can be executed by an application program j. So much input data that storage is exceeded; excess input contains code that takes control of the computer
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (1 review)
Here is the list of computer fraud and abuse techniques matched with the corresponding scenarios 1 Address Resolution Protocol ARP spoofing 1 Insertin...View the full answer

Answered By

Pranav Makode
I am a bachelor students studying at professor ram meghe institute of technology and research. I have a great experience of being an expert. I have worked as an expert at helloexperts and solvelancer as a part time job. I have also worked as a doubt solver at ICAD SCHOOL OF LEARNING, which is in Amravati city. I have also worked as an Freelancer.
I have great experience of helping students, as described above. I can help any students in a most simple and understandable way. I will not give you have any chance for complaint. You will be greatfull to accept me as an expert.
5.00+
1+ Reviews
10+ Question Solved
Related Book For 

Accounting Information Systems
ISBN: 9781292060521
13th Global Edition
Authors: Marshall B. Romney, Paul John Steinbart
Question Posted:
Students also viewed these Business questions
-
Match the computer fraud and abuse technique in the left column with the scenario in the right column. Terms on the left may be used once, more than once, or not atall. 1. Dictionary attack a Spcal...
-
Match the computer fraud and abuse technique in the left column with the scenario in the right column. Terms on the left may be used once, more than once, or not atall. 1. Chipping a. llegally...
-
Match the computer fraud and abuse technique in the left column with the scenario in the right column. Terms on the left may be used once, more than once, or not atall. 1. Bluebugging 2. Bluesnarfing...
-
What are some advantages of sole proprietorship for PODS? What are some of the disadvantages?
-
On July 1, 2010, Brower Industries, Inc. issued $32,000,000 of 10-year, 12% bonds at an effective interest rate of 13%, receiving cash of $30,237,139. Interest on the bonds is payable semiannually on...
-
Identify and explain the fallacies of relevance in the following passages: During World War I, the British government deliberately inflamed the anti-German sentiments of the people with cartoons. One...
-
The two insulated, current-carrying wires in Figure P28.7 cross at right angles, and each carries a current \(I\). The locations labeled 1-4 are all in the plane defined by the wires, with each...
-
On January 1, 2016, Teacher Credit Union (TCU) issued 8%, 20-year bonds payable with face value of $400,000. The bonds pay interest on June 30 and December 31. Requirements 1. If the market interest...
-
1. In the given reaction, XYZ3 2. 3. 4. 5. X+Y+3Z If one mole of each of X and Y with 0.05 mol of Z gives compound XYZ3. (Given: Atomic masses of X, Y and Z are 10, 20 and 30 amu, respectively.) The...
-
On December 1, 2020, Papadopoulos Seasonings had the following account balances. During December, the company completed the following transactions. Dec. 7 Received 3,600 cash from customers in...
-
Fraud perpetrators threaten to harm a company if it does not pay a specified amount of money. What is this computer fraud technique called? a. Cyber-terrorism b. Blackmailing c. Cyber-extortion d....
-
A perpetrator attacks phone systems to obtain free phone line access or uses telephone lines to transmit viruses and to access, steal, and destroy data. What is this computer fraud technique called?...
-
Consider the following reaction: 2 CH 4 (g) C 2 H 2 (g) + 3 H 2 (g) A reaction mixture at 1700 C initially contains [CH 4 ] = 0.115 M. At equilibrium, the mixture contains [C 2 H 2 ] = 0.035 M. What...
-
What countries are negotiating to join the Trans Pacific Partnership (TPP)? What countries may be interested in joining this group? (Use information from the U.S. Trade Representative at www.ustr.gov...
-
A study of the geographic mobility looked at how often adult daughters moved outside the ZIP code in which they were born [14]. The study found that the daughters of immigrants to the United States...
-
In 1993, a member of a presidential task force on food assistance stated If you think that blacks as a group are undernourished, look around at the black athletes on televisiontheyre a pretty hefty...
-
Explain any possible flaws in this conclusion [17]: A drinker consumes more than twice as much beer if it comes in a pitcher than in a glass or bottle, and banning pitchers in bars could make a dent...
-
Explain why these data are not convincing evidence that the way to seize more illegal drugs is to conduct fewer searches: In 2000, [the U.S. Customs service] conducted 61 percent fewer searches than...
-
The plant manager of a plastic pipe manufacturer has the opportunity to use two different routings for a particular type of plastic pipe. Routing 1 uses extruder A. and routing 2 uses extruder B....
-
Consider the setup in Problem 16. Show that the relative speed of the ball and the point of contact on the stick is the same before and immediately after the collision. (This result is analogous to...
-
Figure is a systems flowchart for the first few steps in an order entry process. Some but not all of the controls have been annotated on the flowchart. Figure is a partially completed control matrix...
-
Figure is a systems flowchart for the first few steps in an order entry process. Some but not all of the controls have been annotated on the flowchart. Figure is a partially completed control matrix...
-
Technology Summary 9.1 (pg. 332) describes the impact that pervasive and general controls from Chapter 8 can have on the effectiveness of controls in Figure 9.3 (pg. 323), Figure 9.4 (pg. 325), and...
-
The Wisynco Group is known as the innovators in the manufacturing and distribution industry in Jamaica. The company has many innovations that have been successful both in the local and international...
-
Marketing Objectives . Set marketing plan objectives for Lee's business . Identify at least two S.M.A.R.T. goals (i.e., specific, measurable, achievable, realistic (and relevant to the mission), and...
-
Freeman's services are divided into 6 solution expertise: Programs, Strategy, Creative, Digital, Event Technology, and Logistics. For each solution expertise, select two aspects that interest you the...

Study smarter with the SolutionInn App