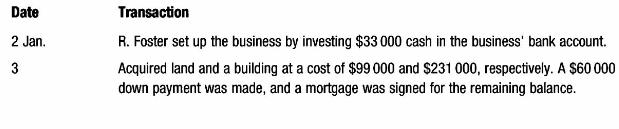
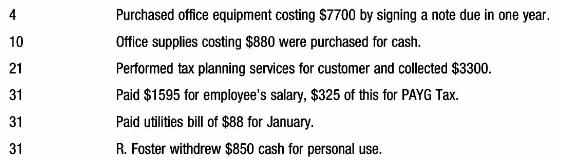
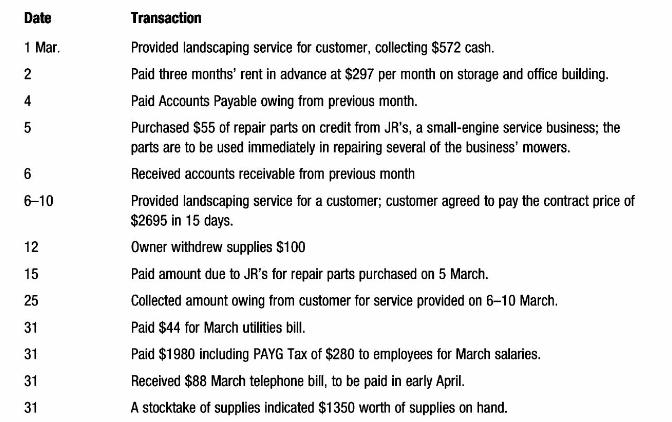
Accounting Information For Business Decisions 2nd Edition Billie Cunningham, Loren A. Nikolai, John Bazley, Marie Kavanagh, Geoff Slaughter, Sharelle Simmons - Solutions
Discover comprehensive solutions and answers for "Accounting Information For Business Decisions, 2nd Edition" by Billie Cunningham and others. Access the online solution manual and answers key, featuring detailed chapter solutions and step-by-step answers to solved problems. Whether you're searching for a test bank or an instructor manual, our resource provides all the questions and answers you need. Download the solutions PDF for free and enhance your understanding of the textbook's concepts. This invaluable resource is perfect for those seeking efficient and effective ways to grasp business accounting principles.
![]()
![]() New Semester Started
Get 50% OFF
Study Help!
--h --m --s
Claim Now
New Semester Started
Get 50% OFF
Study Help!
--h --m --s
Claim Now
![]()
![]()