Question: If the one-time pad cipher (Figure 31.12 in the text) is the simplest and most secure cipher, why is it not used all of the
If the one-time pad cipher (Figure 31.12 in the text) is the simplest and most secure cipher, why is it not used all of the time?
Figure 31.12
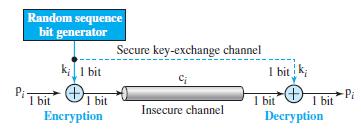
Random sequence bit generator Secure key-exchange channel k;1 bit I bit k; I bit 1 bit Encryption Pi I bit Decryption I bit Insecure channel
Step by Step Solution
3.59 Rating (160 Votes )
There are 3 Steps involved in it
The onetime pad is an ideal but a theoretical cipher it cann... View full answer

Get step-by-step solutions from verified subject matter experts


