Buffers are employed between different levels of memory hierarchy to reduce access latency. For this given configuration,
Question:
Buffers are employed between different levels of memory hierarchy to reduce access latency. For this given configuration, list the possible buffers needed between L1 and L2 caches, as well as L2 cache and memory.
Recall that we have two write policies and write allocation policies, and their combinations can be implemented either in L1 or L2 cache.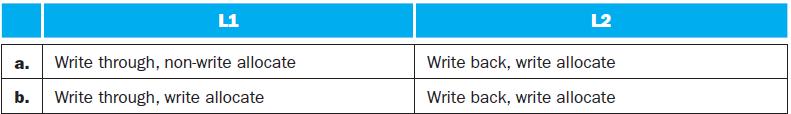
Transcribed Image Text:
L1 a. Write through, non-write allocate b. Write through, write allocate L2 Write back, write allocate Write back, write allocate
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 50% (2 reviews)
The following are the possible buffers needed between L1 and L2 caches as well as L2 cache and memory for the given configuration Between L1 and L2 ca...View the full answer

Answered By

Gauri Hendre
I worked as EI educator for Eduphy India YT channel. I gave online tutorials to the students who were living in the villages and wanted to study much more and were preparing for NEET, TET. I gave tutions for topics in Biotechnology. I am currently working as a tutor on course hero for the biochemistry, microbiology, biology, cell biology, genetics subjects. I worked as a project intern in BAIF where did analysis on diseases mainly genetic disorders in the bovine. I worked as a trainee in serum institute of India and Vasantdada sugar institute. I am working as a writer on Quora partner program from 2019. I writing on the topics on social health issues including current COVID-19 pandemic, different concepts in science discipline. I learned foreign languages such as german and french upto A1 level. I attended different conferences in the science discipline and did trainings in cognitive skills and personality development skills from Lila Poonawalla foundation. I have been the member of Lila poonawalla foundation since 2017. Even I acquired the skills like Excel spreadsheet, MS Office, MS Powerpoint and Data entry.
5.00+
4+ Reviews
10+ Question Solved
Related Book For 

Computer Organization And Design The Hardware Software Interface
ISBN: 9780123747501
4th Revised Edition
Authors: David A. Patterson, John L. Hennessy
Question Posted:
Students also viewed these Computer science questions
-
Recall that we have two write policies and write allocation policies, and their combinations can be implemented either in L1 or L2 cache. Assume the following choices for L1 and L2 caches: L1...
-
For a multilevel exclusive cache (a block can only reside in one of the L1 and L2 caches), configuration, describe the procedure of handling an L1 write-miss, considering the component involved and...
-
Describe the procedure of handling an L1 write-miss, considering the component involved and the possibility of replacing a dirty block. Recall that we have two write policies and write allocation...
-
Giroud plc is considering two alternative investment opportunities. Each of the two projects has an expected life of five years and requires an initial investment of $100,000. A feasibility study...
-
Valentins Acting School produces annual cash flows of $5,000 and is expected to continue doing so in the infinite future. The cost of equity capital for Valentins is 16 percent, and the firm is...
-
Write a method called fromCounts that converts an ArrayIntList of counts into a new ArrayIntList of values as follows. Assume that the list stores a sequence of integer pairs that each pair indicates...
-
Glycerin at \(20^{\circ} \mathrm{C}\) flows upward in a vertical 75 -mm-diameter pipe with a centerline velocity of \(1.0 \mathrm{~m} / \mathrm{s}\). Determine the head loss and pressure drop in a...
-
The general ledger of Red Storm Cleaners at January 1, 2021, includes the following account balances: The following is a summary of the transactions for the year:1. March 12 Provide services to...
-
For sgupta20: 700 words, Original Work, References Included, Plagerism free. In text citation included. Write a paper in which you examine the field of abnormal psychology. Address the following...
-
Assuming that the L1 hit time determines the cycle times for P1 and P2, what are their respective clock rates? In this exercise, we will look at the different ways capacity affects overall...
-
What is the cache line size (in words)? For a direct-mapped cache design with a 32-bit address, the following bits of the address are used to access the cache. a. b. Tag 31-10 31-12 Index 9-5 11-6...
-
Consider the melting-point data in Exercise 10-25. Do the sample data support a claim that both alloys have the same variance of melting point? Use = 0.05 in reaching your conclusion. Exercise 10-25...
-
How is spirituality understood in the Shinto religion ? Explain
-
1. Amabile theorized that four things can restrict creativity: evaluation, rewards, competition, and constraints. Describe why each of these might affect the creative process and give one specific...
-
Essentially is a brief exploration of the primary intersections between the Bill of Rights and the practice of commerce in the United States. The chapter primarily focuses on freedom of religion,...
-
Identify the four identity statuses that researchers use to evaluate progress in identity development. Describe the cognitive style typically used by adolescents in each of these statuses. How does...
-
For this Reflection, rewatch (watch) the film "Reflecting on Anti-Bias Education in Action: The Early Years". The film can be found in Module 6. What can educators learn from watching the film? Be...
-
Match the following terms to their definitions. 1. Direct labor plus manufacturing overhead 2. Prepared by department for EUP, production costs, and assignment of costs 3. Equivalent units of...
-
Express mass density in kg/m3 and weight density in lb/ft3. 1. Find the mass density of a chunk of rock of mass 215 g that displaces a volume of 75.0 cm3 of water. 2. A block of wood is 55.9 in. x...
-
What are some reasons that CSMA/CD cannot be used in a wireless LAN?
-
Write and test a program that simulates the bit stuffing and bit unstuffing as shown in Figure 11.4. Figure 11.4 Bit stuffing and unstuffing Data from upper layer 0001111111001111101000 Stuffed Frame...
-
In Figure 15.24, two wireless networks, BSS1 and BSS2, are connected through a wired distribution system (DS), an Ethernet LAN. Assume station A in BSS1 needs to send a data frame to station C in...
-
Example: The strength required for Orowan dislocation bypass is 200 MPa in an alloy when the interparticle spacing is 500 nm. In the same alloy, if the interparticle spacing is reduced to 200 nm, the...
-
At the instant shown, the angular velocity of crank OB is 130 rpm in the counterclockwise direction. Know that gear C is fixed. 12 in. 0 8 in. C Problem 15.027.a Angular velocity of the planetary...
-
Part A - Moment due to a force specified by magnitude and endpoints Learning Goal: To use the vector cross product to calculate the moment produced by a force, or forces, about a specified point on a...

Study smarter with the SolutionInn App