Question: A nonmaskable interrupt (NMI) is triggered by an input pin to the processor. When the pin is asserted, the current instruction should finish, then the
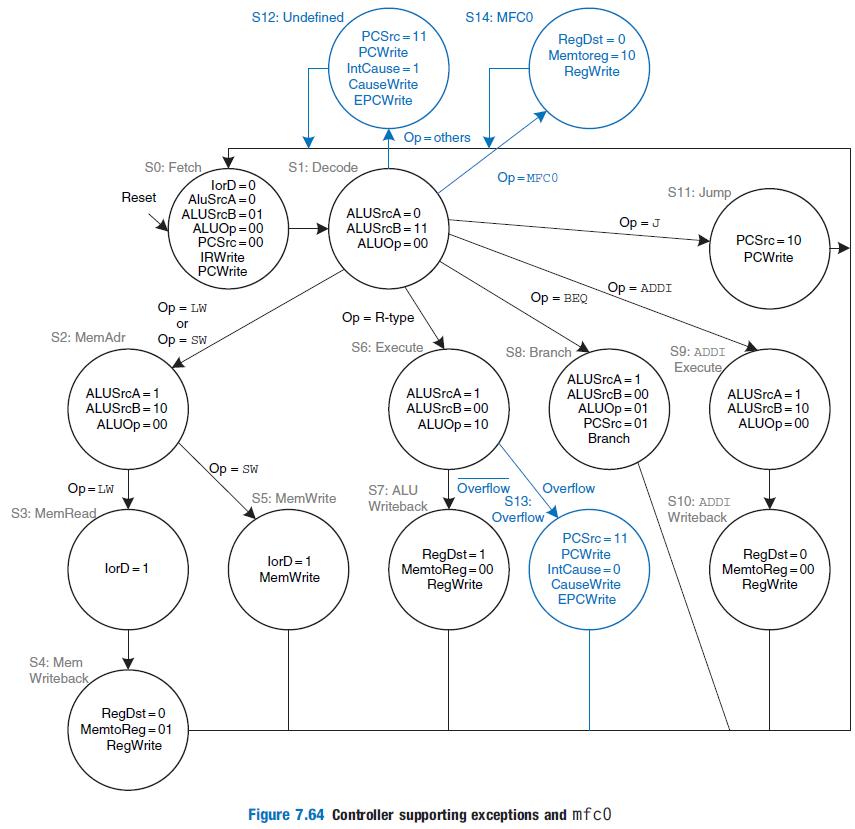
A nonmaskable interrupt (NMI) is triggered by an input pin to the processor. When the pin is asserted, the current instruction should finish, then the processor should set the Cause register to 0 and take an exception. Show how to modify the multicycle processor in Figures 7.63 and 7.64 to handle nonmaskable interrupts.
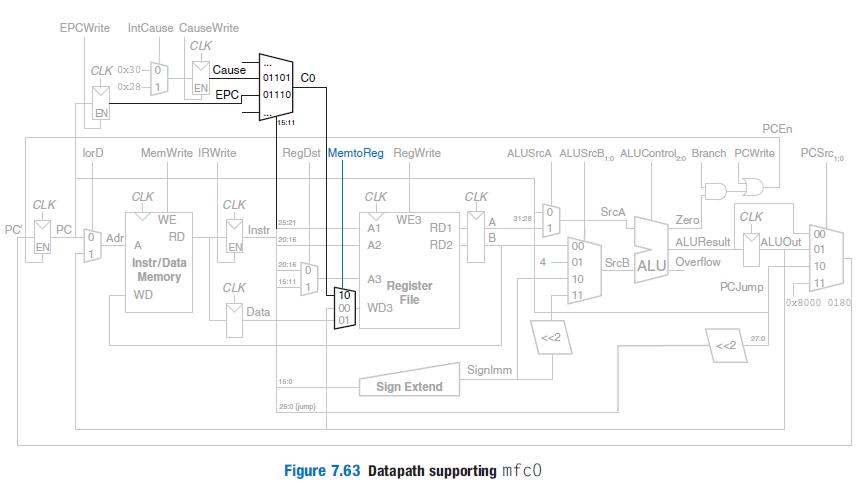
EPCWrite IntCause CauseWrite CLK CLK Ox30- 0 Cause 01101 CO Ox28 EN 01110 EN 15:11 PCEN RegDst MemtoReg RegWrite PCSrc,0 lorD MemWrite IRWrite ALUSrcA ALUSrcB,, ALUControl, Branch PCWrite 10 CLK CLK CLK CLK CLK SrcA WE WE3 Zero CLK 3128 25:21 PC PC A1 RD1 O Adr A Instr 20:16 00 RD ALUResult ALUOut 01 EN EN A2 RD2 00 Instr/Data 4 01 SrcB ALU Overflow 20:18 10 Memory Register File 15:11 10 PCJump 11 CLK WD 10 00 11 Ox8000 0180 Data WD3 01 <
Step by Step Solution
3.52 Rating (165 Votes )
There are 3 Steps involved in it
PC CLK EPCWrite IntCauseCauseWrite CLK PC 0x30 CLK 0x28 EN lorD 0x02 Adr MemWrite IRWrite CLK A WE W... View full answer

Get step-by-step solutions from verified subject matter experts


