;The main reason of why we use passcode locks on mobile devices is : Increase the...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
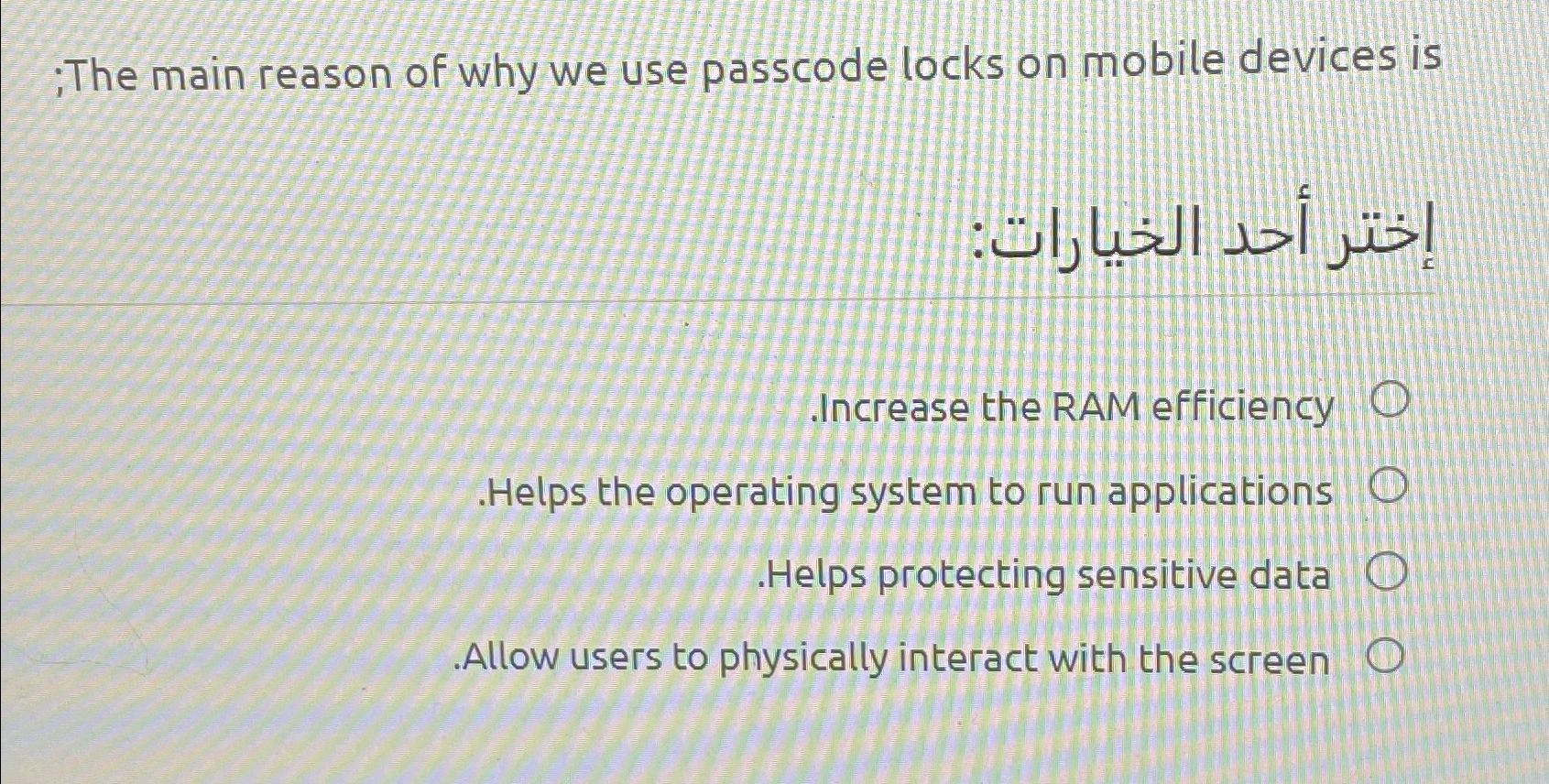
;The main reason of why we use passcode locks on mobile devices is : Increase the RAM efficiency .Helps the operating system to run applications O Helps protecting sensitive data O .Allow users to physically interact with the screen O ;The main reason of why we use passcode locks on mobile devices is : Increase the RAM efficiency .Helps the operating system to run applications O Helps protecting sensitive data O .Allow users to physically interact with the screen O
Expert Answer:
Answer rating: 100% (QA)
The question is about the main reason why we use passcode locks on mobile devices Among the presente... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these programming questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
Select the best response. What trend can be related to a major employer closing a business? Property values falling and people moving from a community. A rise in slips, trips and falls. New...
-
Restaurants do a large volume of business by credit and debit cards. Suppose Summer, Sand, and Castles Resort restaurant had these transactions on January 28, 2018: National Express credit card sales...
-
For each case, differentiate the set of parametric equations to obtain the second derivative d 2 y/dx 2 . a. x = t 2 , y = 3t + 1 b. x = e t , y = t 2
-
Consider the following cash flow diagram. What is the value of \(X\) if the internal rate of return is 15 percent? a. \(\$ 246\) b. \(\$ 255\) c. \(\$ 281\) d. \(\$ 290\) 0 $400 X X 1 2
-
Pearl Products Limited of Shenzhen, China, manufactures and distributes toys throughout South East Asia. Three cubic centimeters (cc) of solvent H300 are required to manufacture each unit of...
-
Problem 5. [20 pts] Verify Green's Theorem for the following vector field and region D. Namely, compute both, the line integral and the double integral. x1 1. (10pts) F (1,-1). and D is the square...
-
Barry Bird opened the Barry Bird Basketball Camp for children ages 10 through 18. Campers typically register for one week in June or July, arriving on Sunday and returning home the following...
-
Research one aspect of international markets. Assess and analyse your findings.
-
This is a regional government's expenditure whose benefits exceed one fiscal year and will augment regional assets or assets in the form of infrastructure, equipment, and other fixed assets. a....
-
Briefly discuss the key features of the Gold Standard system and explain why it might be unlikely for a country under this system to experience sustained balance of payment deficit problems.
-
Development of Skills The development of skills is of utmost importance to learners. Skill Hence, schools need to provide for systematic and planned instruction that development involves tasks which...
-
1. The IRR method is easier to use because it does not require the calculation of the cost of capital. True False
-
A lightly loaded 360 journal bearing 3.8 in. in diameter and 4.5 in. long operates with a radial clearance of 0.006 in. and a speed of 1100 rpm. SAE 10 oil is used at 150F. Determine the power loss...
-
In the General Assembly of TURKO firm, it was decided to pay 100% free, 75% capital increase and distribute 1.25 TL dividend per share. It has been announced that the pre-emptive rights will be used...
-
Write a program to move a signed number from smaller register to bigger register. Hint: movzx ax, bl Topic: Data Related Operators and Directives in assembly language
-
Which of the following is an event that triggers alarms when no actual attacks are in progress? a. Evasion b. False positive c. False attack stimulus d. False negative
-
I. Detail that the purpose of this mode is to encrypt all traffic that will traverse an unsecured network, and the receiving server decrypts the packet to be able to send the final address. II....
-
Describe malware as malicious code or malicious software. Point out that other attacks that use software, such as redirect attacks and denial-of-service attacks, also fall under this threat. Note...
-
The sequence in Figure P2.2 represents a ball rolling into a wall and bouncing off of it. The ball is \(10 \mathrm{~mm}\) in diameter. Make a graph showing the distance from the leading edge of the...
-
You walk \(3.2 \mathrm{~km}\) to the supermarket and then back home. What is your distance traveled? What is your displacement?
-
Your class observed several different objects in motion along different lines. Figure P2.5 shows some of the graphs other students made of the events. They have labeled the horizontal axis "time" and...

Study smarter with the SolutionInn App


