Data Structures And Other Objects Using Java 4th Edition Michael Main - Solutions
Discover comprehensive solutions and answers key for "Data Structures And Other Objects Using Java 4th Edition" by Michael Main. Our online resource provides a complete solution manual, offering step-by-step answers and solved problems to enhance your understanding. Access chapter solutions and test bank questions and answers, tailored for both students and instructors. The instructor manual and textbook resources are available for free download, ensuring you have the best materials at your fingertips. Elevate your learning experience with our expertly crafted solutions PDF, designed to support your academic success.
![]()
![]() New Semester Started
Get 50% OFF
Study Help!
--h --m --s
Claim Now
New Semester Started
Get 50% OFF
Study Help!
--h --m --s
Claim Now
![]()
![]()


![FIGURE 14.4 Depth-First Search Implementations public static void depthFirstRecurse (Graph g, int v, boolean[ ] marked) { int[ ] connections = g.neighbors(v); int i; marked [v] = true; System.out.println(g.getLabel(v)); // Traverse all the neighbors, looking for unmarked vertices: for (int nextNeighbor : connections) { if (!marked [nextNeighbor]) depthFirstRecurse(g, nextNeighbor,](https://dsd5zvtm8ll6.cloudfront.net/si.question.images/images/question_images/1605/8/5/7/9455fb77299a63271605857944105.jpg)
![void mergesort( int data[ ], int first, int n, int temp[ ] ); // Precondition: data[first] through // data[first+n-1] are array elements in no // particular order. The temp array has // locations temp[first] through // temp[first+n-1]. // Postcondition: The elements // datalfirst] through data[first+n-1] // have been rearranged so](https://dsd5zvtm8ll6.cloudfront.net/si.question.images/images/question_images/1605/8/5/6/1985fb76bc6d4a731605856197578.jpg)
![private static void heapifySubtree( int[ ] data, int root0fSubtree, int n // Precondition: data is an array with at least // n elements, and rootOfSubtree < n. We will // consider data to represent a complete // binary tree, and in this representation the // node at data[rootOfSubtree] is the](https://dsd5zvtm8ll6.cloudfront.net/si.question.images/images/question_images/1605/8/5/6/2175fb76bd9279981605856215830.jpg)
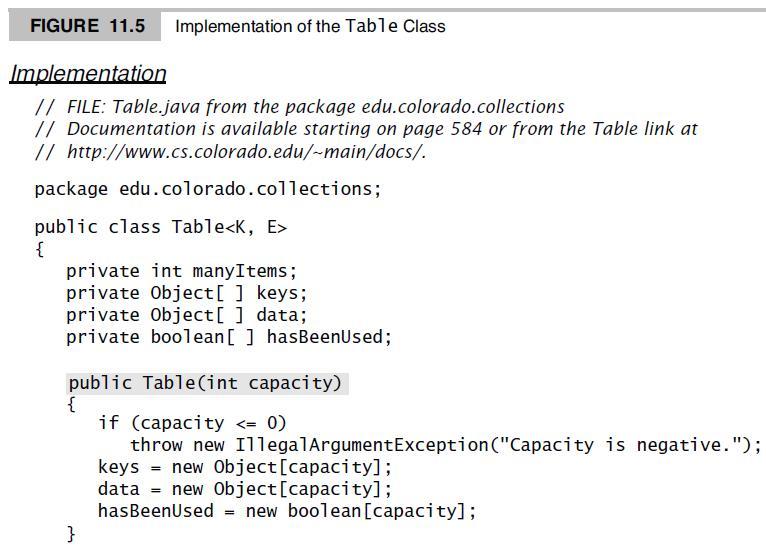
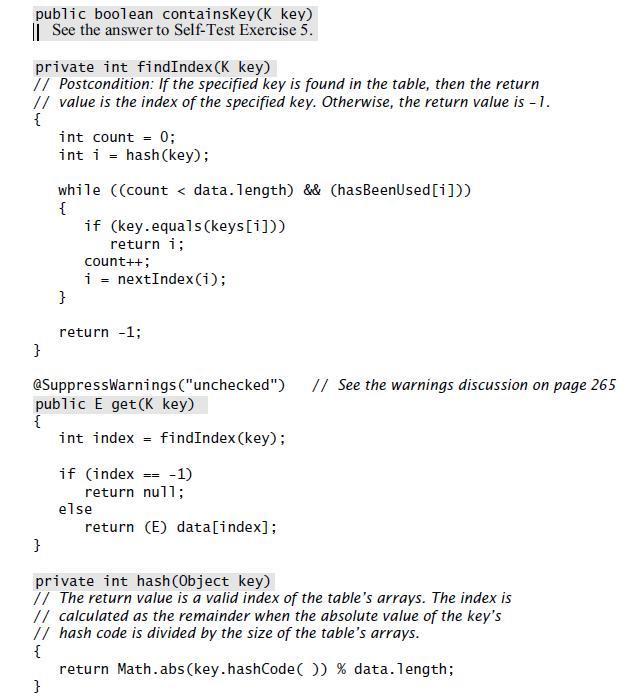
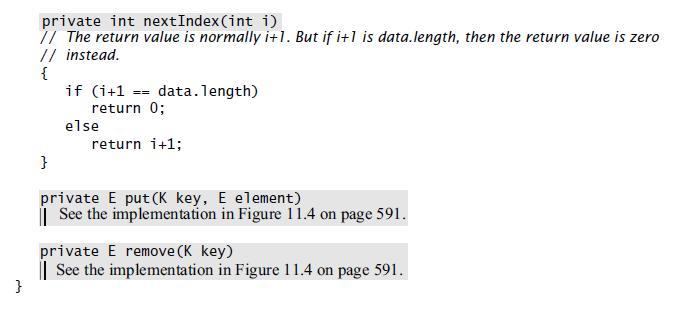
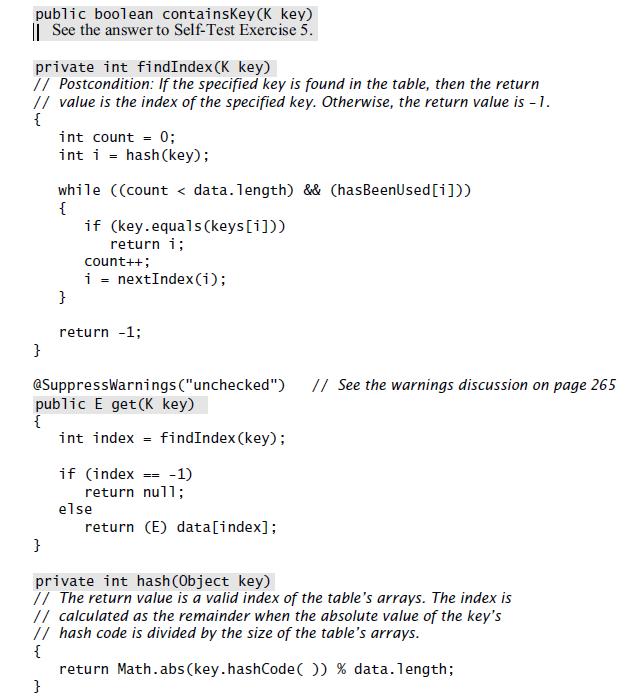
![FIGURE 11.5 Implementation of the Table Class Implementation // FILE: Table.java from the package edu.colorado.collections // Documentation is available starting on page 584 or from the Table link at // http://www.cs.colorado.edu/~main/docs/. package edu.colorado.collections; public class Table { private int manyItems; private Object[ ] keys; private Object[ ] data; private boolean[](https://dsd5zvtm8ll6.cloudfront.net/si.question.images/images/question_images/1605/8/5/5/5505fb7693e5eeed1605855548802.jpg)
![FIGURE 9.8 The Animal-Guessing Program Java Application Program // FILE: Animal.java // This animal-guessing program illustrates the use of the binary tree node class. import edu.colorado.nodes.BTNode; // For BTNode import java.util.Scanner; public class Animal { private static Scanner stdin = new Scanner(System.in); public static void main(String[ ] args) { BTNode](https://dsd5zvtm8ll6.cloudfront.net/si.question.images/images/question_images/1605/8/5/4/0525fb763640c1d91605854050483.jpg)
![FIGURE 9.8 The Animal-Guessing Program Java Application Program // FILE: Animal.java // This animal-guessing program illustrates the use of the binary tree node class. import edu.colorado.nodes.BTNode; // For BTNode import java.util.Scanner; public class Animal private static Scanner stdin = new Scanner(System.in); public static void main(String[ ] args) { BTNode root;](https://dsd5zvtm8ll6.cloudfront.net/si.question.images/images/question_images/1605/8/5/1/0445fb757a49f4a81605851036991.jpg)