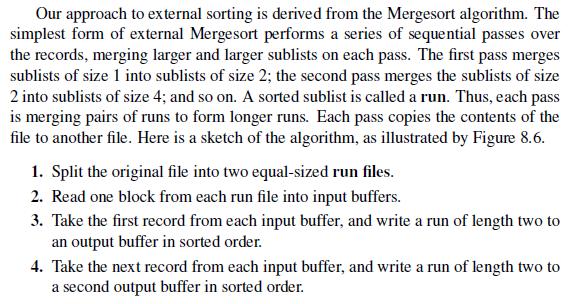
![]()
![]() New Semester Started
Get 50% OFF
Study Help!
--h --m --s
Claim Now
New Semester Started
Get 50% OFF
Study Help!
--h --m --s
Claim Now
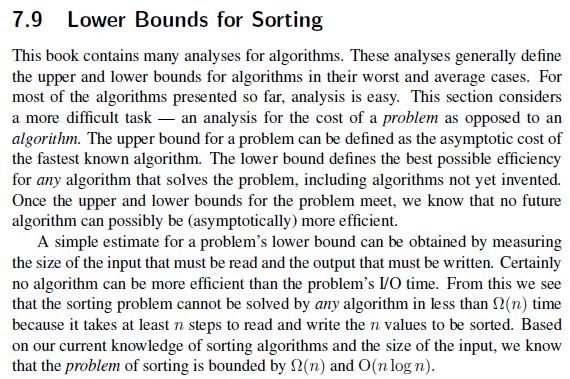
![]()
![]()


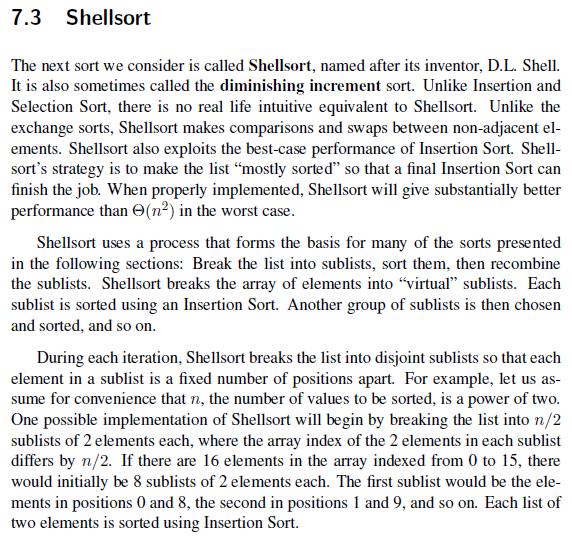
![/** General Tree class implementation class ParPtrTree { private Integer [] array; public ParptrTree (int](https://dsd5zvtm8ll6.cloudfront.net/images/question_images/1705/3/1/9/05065a51a8aacc2f1705319051189.jpg)
![Parent(r) = [ (r - 1)/2] ifr / 0. Left child(r) = 2r + 1 if 2r +1](https://dsd5zvtm8ll6.cloudfront.net/images/question_images/1705/3/1/8/39965a517ffd343d1705318399764.jpg)
![List SORTK (List L) { List sub [k]; // To hold the sublists if (L. length() style=](https://dsd5zvtm8ll6.cloudfront.net/images/question_images/1705/3/2/2/01765a5262195a1c1705322017648.jpg)