Question: 5. Consider the following protocol, where KAB is a shared symmetric key, CLNT and SRVR are constants, and the session key is K=h(S, RA, RB).
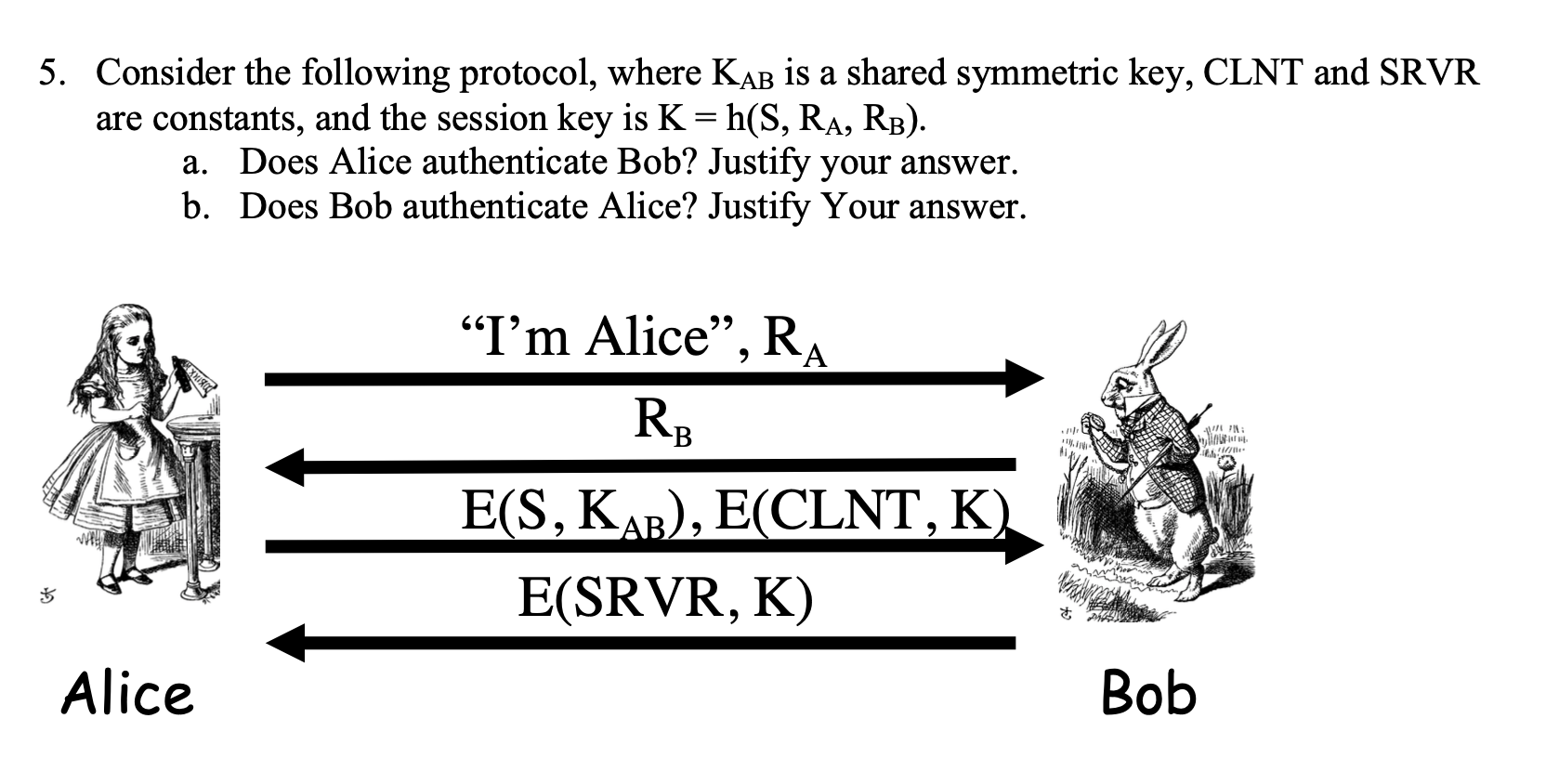
5. Consider the following protocol, where KAB is a shared symmetric key, CLNT and SRVR are constants, and the session key is K=h(S, RA, RB). a. Does Alice authenticate Bob? Justify your answer. b. Does Bob authenticate Alice? Justify Your answer. I'm Alice, RA RB 11!! E(S, KAB), E(CLNT, K) E(SRVR, K) Alice Bob
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


